Blast Radius - Introducing Multiple Source Types
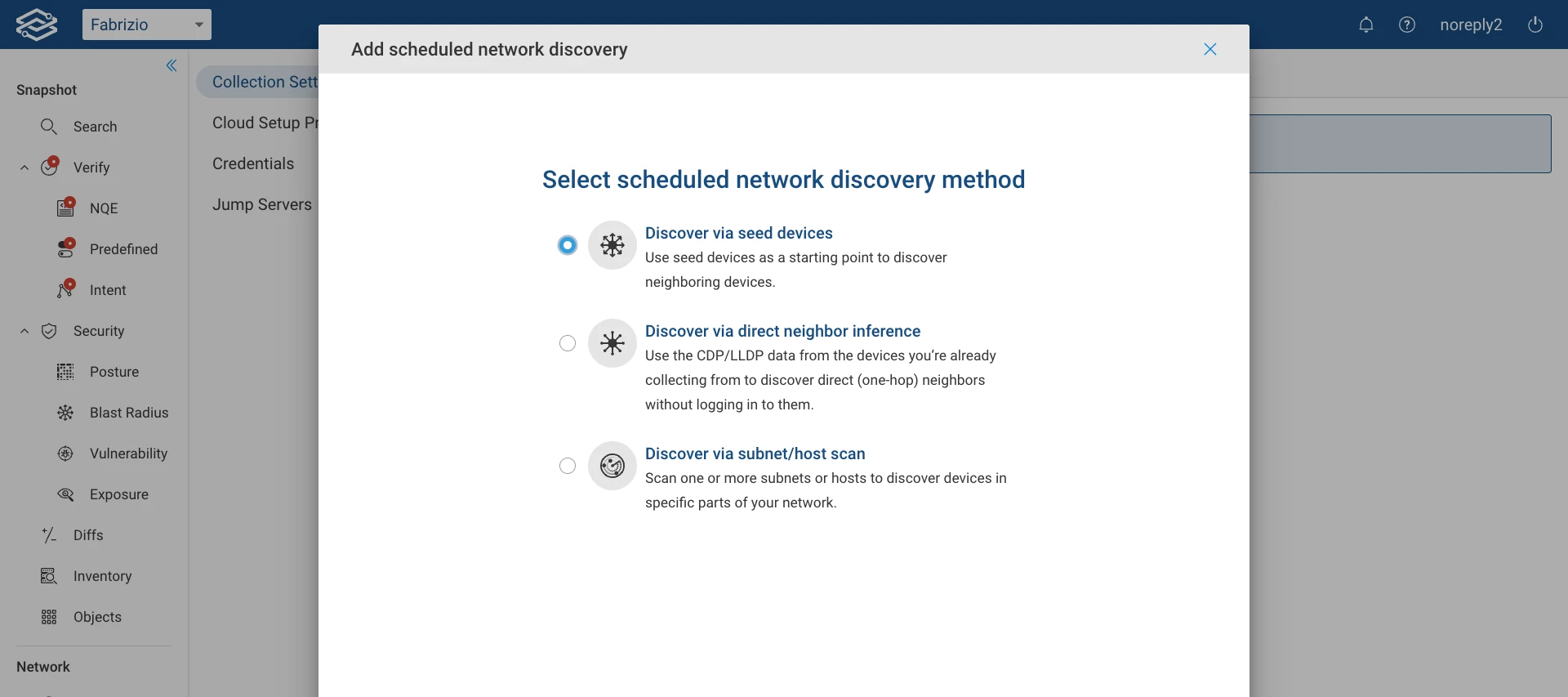
We're excited to introduce the latest update to Blast Radius with the release of 24.2, now enabling the use of multiple source types for Blast Radius computations. In previous releases, Blast Radius was confined to computing the blast radius with a single host. With 24.2, you can now employ a variety of source types for Blast Radius computations, providing a more comprehensive analysis of network security.The ability to compute the blast radius from different source types is crucial for network security teams. It offers a deeper understanding of potential vulnerabilities and enhances effective threat mitigation strategies. In the event of a compromised host, security teams need to understand how an attacker can move laterally within the network. Blast Radius now offers a comprehensive analysis of all reachable hosts or subnets from any source location or entity in the network. This includes detailed insights into specific IP protocols, Layer 4 ports, and Layer 7 App IDs.Whether analyzing traffic flow from the Internet, a specific security zone, or a network device, Blast Radius empowers network and security professionals to evaluate the impact of compromised sources within the network. This understanding is vital for assessing security vulnerabilities and preventing potential attacks.The source types now available with 24.2 are:Device Interface Security zone Device VRF Host alias Device alias Interface alias Subnet locationScreenshot displaying reachability results of a Blast Radius searchTo get started, navigate to the Blast Radius application within the fwd.app, select your desired sources, and click Search to begin analyzing your network.For more information, please refer to the Blast Radius section within Forward Docs.