Aug 17, 2023
In-app What’s New
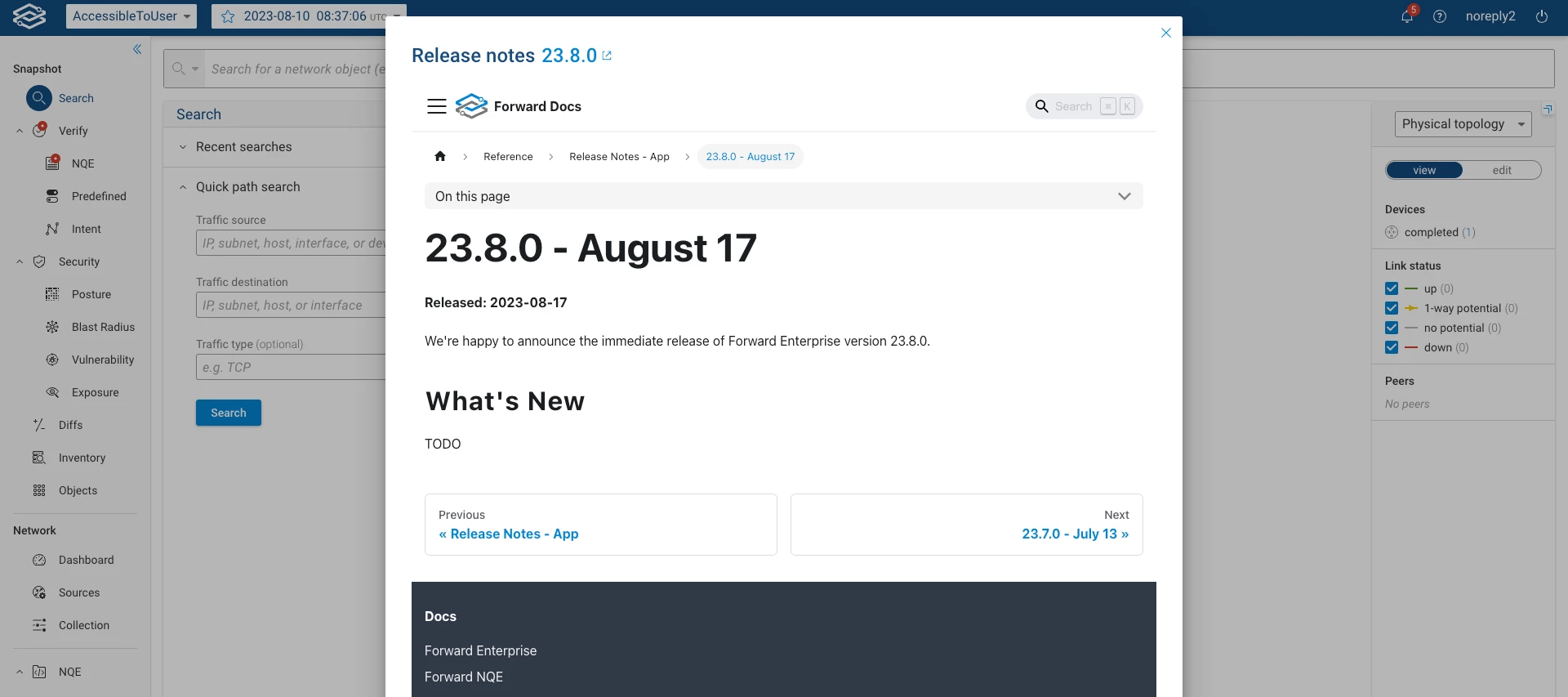
Starting with version 23.8, a dialog box illustrating the Release Notes will appear when you open a fresh tab or window after the system has been updated to the latest major version of the Forward platform.The goal of this dialog box is to keep the users informed about the latest enhancements and features of the Forward platform, in addition to any fixed bugs.
Related products:Platform