We’re excited to introduce the release of Forward Enterprise version 24.9.0, which brings powerful new features and enhancements designed to streamline network operations, improve security analysis, and boost data processing capabilities. Here’s an in-depth look at the latest additions:
Forward AI – NQE Doc and Summary AI Assist
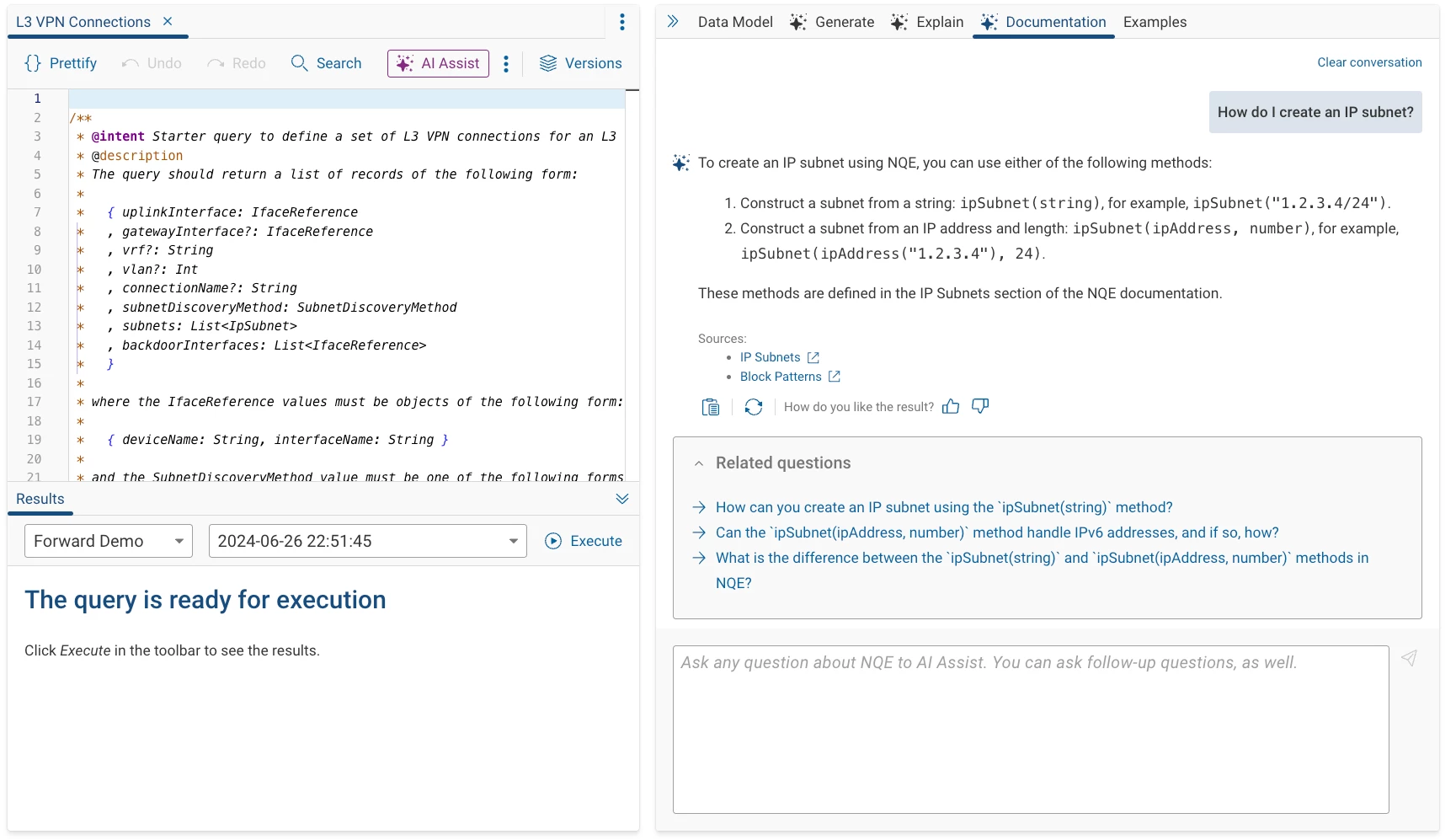
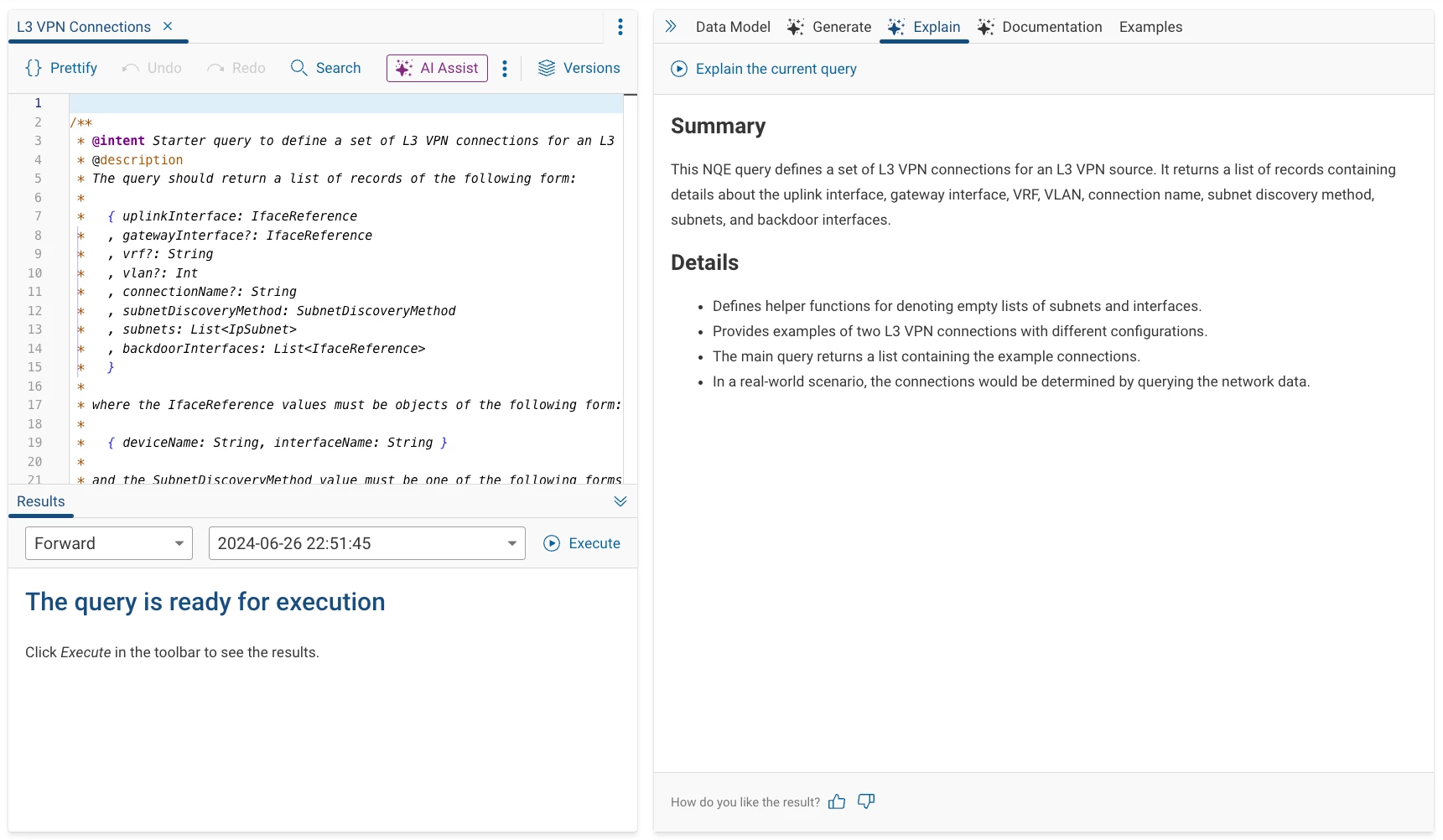
This release marks a significant milestone in Forward’s AI journey with the general availability of NQE Documentation (Doc) AI Assist and NQE Summary AI Assist.
-
NQE Doc AI Assist helps users quickly access information from the NQE documentation via a natural language interface. Just ask questions about any syntax or functions, and the AI will pull the relevant answers with reference links to the documentation. Users can also engage in a conversation by asking follow-up questions.
-
NQE Summary AI Assist breaks down complex NQE queries, explaining what each component of a query does in plain language. This feature helps users of all experience levels to better understand existing queries, ultimately speeding up query creation and optimization.
Note: These Forward AI features are available exclusively to SaaS customers. All data used by the AI Assist tools is kept secure and confidential, stored within Forward's AWS-hosted environment.
Security - Vulnerability Analysis for Palo Alto Devices
Proactive vulnerability management is critical for maintaining a secure network infrastructure. With version 24.9, Forward Enterprise extends its config-based vulnerability analysis to Palo Alto devices, building on its existing vulnerability management tools.
The Vulnerability Management feature helps identify and prioritize security risks based on CVEs (Common Vulnerabilities and Exposures), but it goes a step further by analyzing device configurations. This helps distinguish between potential vulnerabilities and real ones based on actual device configurations, providing a more accurate assessment of network risks.
Security - STIGs Verification for Juniper Devices
STIGs (Security Technical Implementation Guides) are essential for ensuring compliance with DISA’s stringent security guidelines. In this release, Forward Enterprise introduces the ability to use tag-based overrides for STIGs verification on Juniper devices.
This is valuable for devices that might be performing non-standard roles. By using tags, users can modify the STIG verification process to align with a device's actual operational role, improving compliance and security accuracy.
Data Analysis – NQE Date and Time Datatypes
24.9 enhances NQE's data processing capabilities by introducing new date and time datatypes:
- Duration: An interval of time.
- Date: A calendar date.
- Timestamp: A down to the second record of the time of occurrence of a particular event.
These new datatypes make it easier to handle time-based data in queries, providing more detailed insights into network behavior over time.




