Released: 2024-11-19
We’re excited to announce the release of 24.11.0, introducing impactful updates to enhance operational efficiency, streamline compliance, and bolster network security workflows. See the full release notes for Forward Enterprise version 24.11.0.
What’s New:
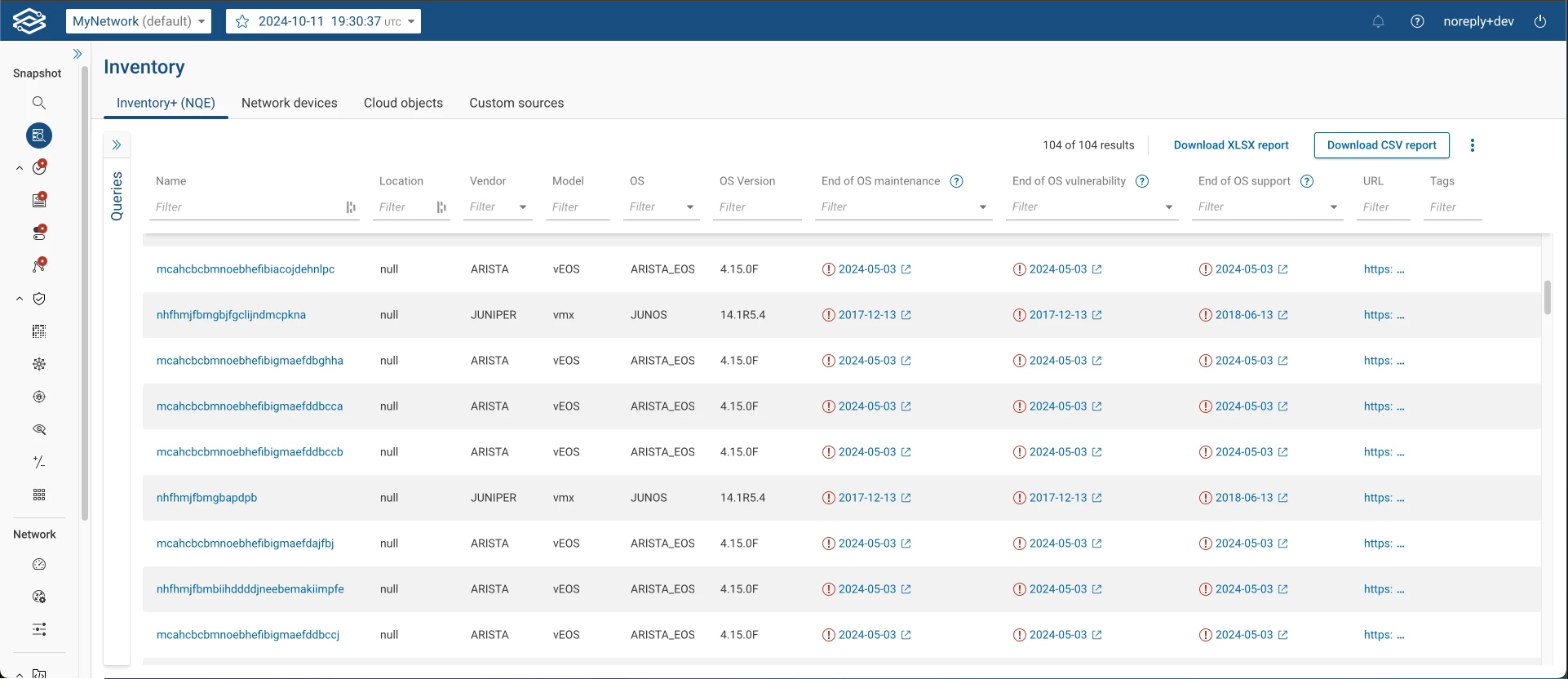
Data Analysis - End of Life data in NQE
Understanding the lifecycle of your network infrastructure is critical for risk management and cost optimization. The first iteration of in-app EOL analysis focuses on identifying outdated operating systems for the following vendors and OSs:
- Cisco: IOS, IOS-XE, IOS-XR, NX-OS
- Arista: EOS
- Juniper: Junos OS
- Palo Alto: PAN-OS
Conducting a robust end-of-life (EOL) data analysis on network infrastructure can deliver significant business value:
- Risk Mitigation: Identify outdated OS versions and reduce potential vulnerabilities.
- Enhanced Security Posture: Prioritize upgrades for unsupported systems.
- Cost Efficiency: Optimize budgets by addressing aging infrastructure.
This feature is available as a dedicated table in the Inventory+ app. Future updates will expand the analysis to additional vendors and hardware components.
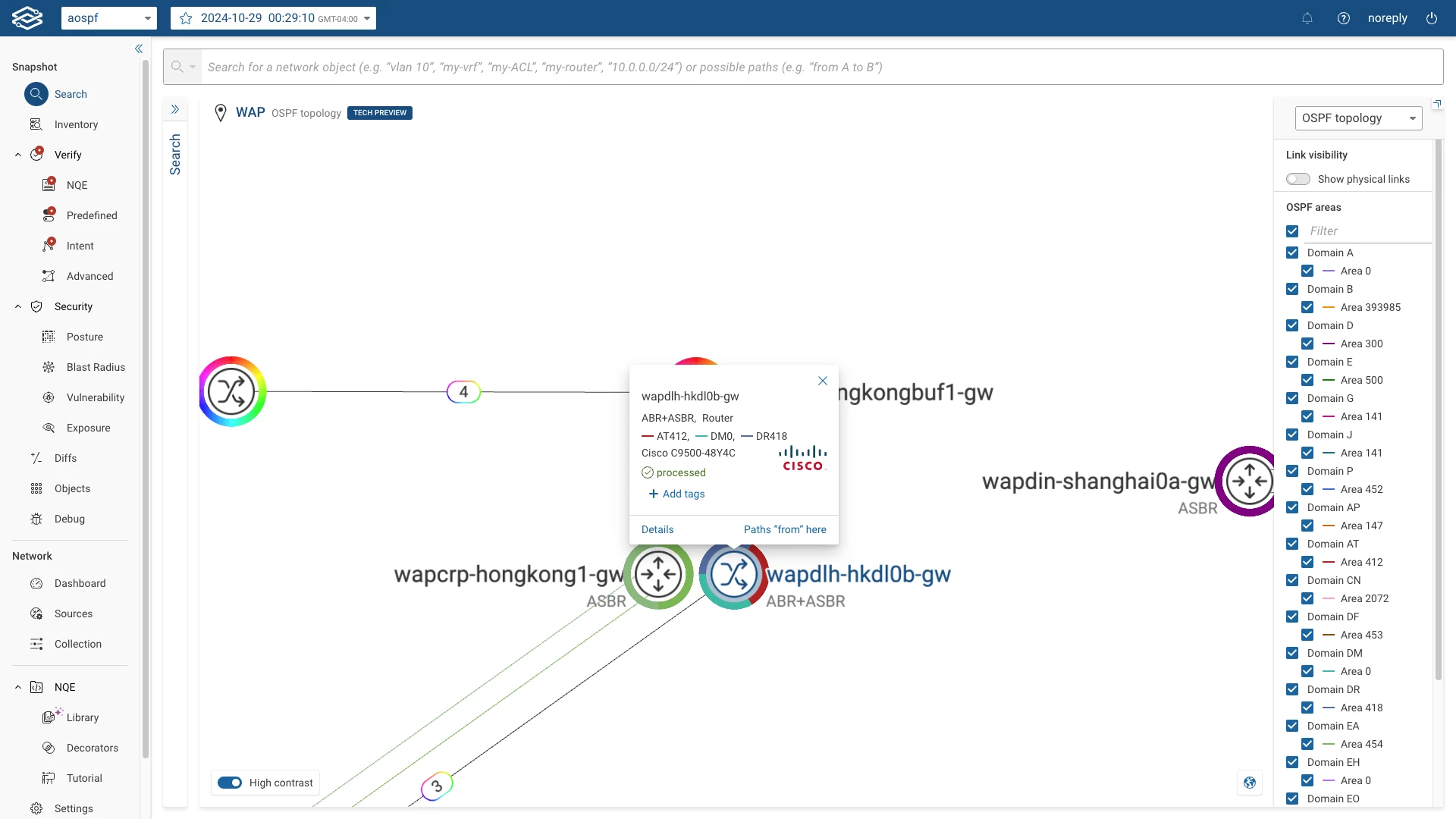
Topology - OSPF layer
Visualizing network topology by protocol layers provides a focused view for enhanced troubleshooting and collaboration. The OSPF layer topology visualization is now available, with support for:
- Vendors: Cisco (ASA, NX-OS, IOS/IOS-XE, IOS-XR), Arista, SilverPeak, Dell SONiC, HPE, and Palo Alto.
Key Benefits:
- Faster Troubleshooting: Isolate and resolve protocol-specific issues.
- Improved Visibility: Gain a clearer understanding of OSPF-specific network operations.
- Enhanced Collaboration: Support cross-team workflows and training with targeted views.
Security - STIGs Export in CKLB Format
Compliance with DISA’s Security Technical Implementation Guides (STIGs) is crucial for securing networks and achieving Authorization to Operate (ATO). This release introduces the ability to export STIG results in the cklb format, simplifying compliance workflows.
Key Features:
- Automates STIG check verifications for supported devices.
- Exports results enriched with device-specific data (e.g., name, IP address, MAC address).
- Bundles results as a ZIP archive with individual cklb files for each device.
The exported files are compatible with DISA’s STIG Viewer and eMASS system, streamlining the compliance process from verification to reporting.
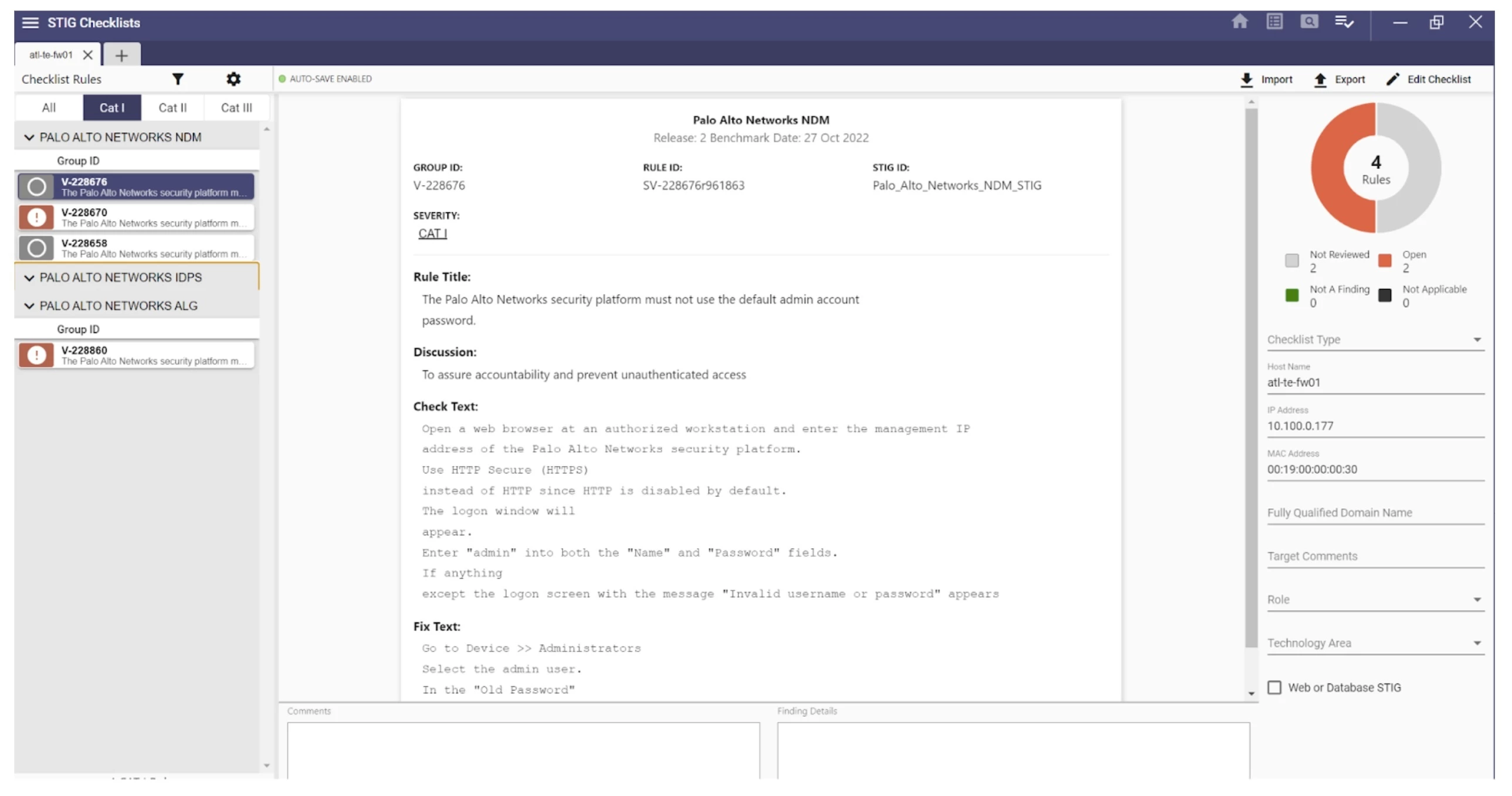
Security - STIGs for Palo Alto devices
The release 24.11 introduces hundreds of new STIG checks in support of the STIG benchmarks for the Palo Alto devices. The specific new STIGs supported are as follows:
- Palo Alto Networks ALG (Application Layer Gateway)
- Palo Alto Networks IDPS (Intrusion Detection and Prevention System)
- Palo Alto Networks NDM (Network Device Management)
Security - CVE base score and published date
Adding CVE Published Dates and CVSS Base Scores to NQE makes vulnerability management easier. These updates help security teams prioritize vulnerabilities based on severity and recency.
- CVE Published Date: Highlights recent vulnerabilities for prioritization.
- CVSS Base Score: Displays the highest available CVSS score (e.g., v4, v3, or v2).
Forward Library Additions at /Forward Library/Security/CVEs/Vendor
foreach cve in network.cveDatabase.cves
foreach vendorInfo in cve.vendorInfos
select {
"CVE ID": cve.cveId,
Vendor: vendorInfo.vendor,
"Publication Date": vendorInfo.publicationDate,
Severity: vendorInfo.severity,
"Base Score": vendorInfo.baseScore,
"Base Score V2": vendorInfo.baseScoreV2,
"Base Score V3": vendorInfo.baseScoreV3,
"Base Score V4": vendorInfo.baseScoreV4,
Description: vendorInfo.description
}




