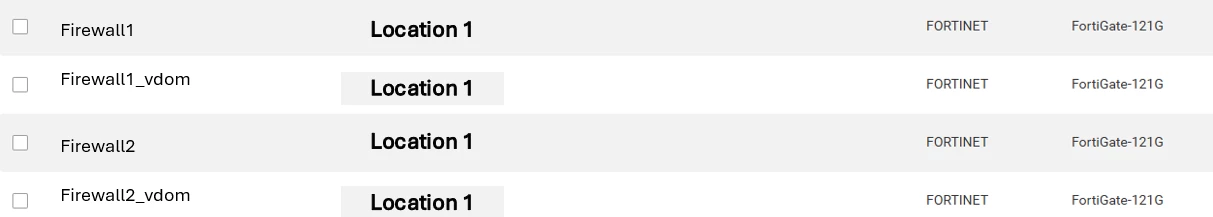
Forward brings in Fortinet firewalls as the device its self and the VDOM’s this becomes challenging when you need to validate the tacacs configuration for the physical device this means quite often the vdoms or even the root vdom will fail even though tacacs is configured on the device.
The simple solution is to add a permitted violation list, however this needs to be maintained manually there must be a better solution surely?
userTacacs =
```
config user tacacs+
edit "TACACS"
set server [server 1 IP Address]
set secondary-server [server 2 IP Address]
set key ENC {string}
set secondary-key ENC {string}
set authorization enable
next
end
```;
systemAdmin =
```
config system admin
edit "tacacs"
set remote-auth enable
set accprofile "no_access"
set vdom {vdoms:string}
set wildcard enable
set remote-group "TACACS_ACCESS"
set accprofile-override enable
```;
foreach device in network.devices
where device.platform.vendor == Vendor.FORTINET
foreach command in device.outputs.commands
where command.commandText == "show user tacacs+" // Retrieve only the tacacs user.
let tacacsOutput = command.response
let tacacsConfig = parseConfigBlocks(OS.OTHER,tacacsOutput)
let userMatches = blockMatches(tacacsConfig, userTacacs)
let userResult = if length(userMatches) == 0
then "User tacacs+ configuration is not standard"
else ""
let sysAdminMatches = blockMatches(device.files.config,systemAdmin)
let sysAdminResult = if length(sysAdminMatches) == 0
then "System Admin tacacs configuration is not standard"
else ""
let result = if userResult != "" && sysAdminResult == ""
then userResult
else if userResult == "" && sysAdminResult != ""
then sysAdminResult
else if userResult != "" && sysAdminResult != ""
then userResult + " and "+sysAdminResult
else "No issues found"
select {
Device: device.name,
violation: length(userMatches) == 0 || length(sysAdminMatches) == 0,
Reason_for_violation:result,
User_Matches: (foreach match in userMatches
select match.blocks),
Admin_Matches: (foreach match in sysAdminMatches
select match.blocks)
}